Decoding Qkfzzu1lbnvinhp4dlhz: What Does It Really Mean?
The exploration of Qkfzzu1lbnvinhp4dlhz reveals a complex digital artifact. This 20-character string combines letters and numbers, hinting at a sophisticated encoding method. Its structure suggests potential ties to contemporary communication trends, particularly in decentralization and information autonomy. Understanding its implications requires examining its origins and possible applications. What secrets does this cryptographic construct hold, and how might it shape future technological interactions? The answers may lie in a deeper analysis.
The Origins of Qkfzzu1lbnvinhp4dlhz
The concept of Qkfzzu1lbnvinhp4dlhz emerges from a complex interplay of technological advancements and cultural influences.
Its historical context reveals a convergence of digital linguistics and cryptographic methodologies, tracing linguistic roots that reflect societal shifts toward decentralized communication.
This notion encapsulates the desire for autonomy in expression, illustrating how technological evolution can foster unique forms of interaction while challenging traditional language structures.
Analyzing the Structure of the String
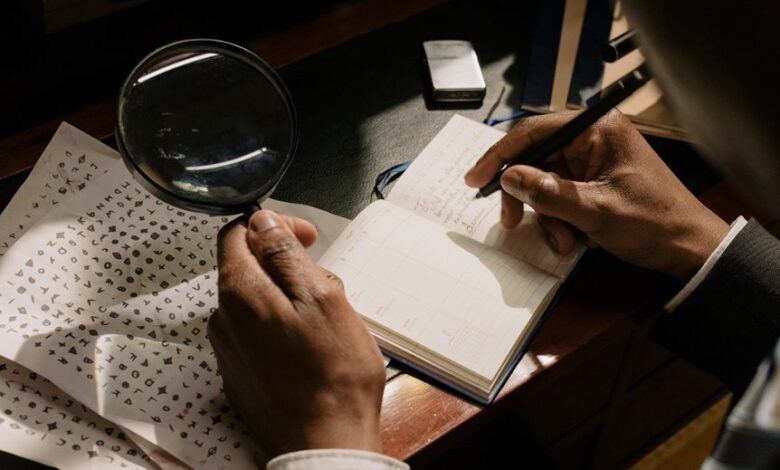
The structure of the string Qkfzzu1lbnvinhp4dlhz warrants a detailed examination of its character composition, which may reveal insights into its encoding techniques.
By identifying the frequency and types of characters present, one can explore potential encoding methods utilized in its formation.
Additionally, interpretations of its meaning may emerge from understanding both the structural elements and their arrangement within the string.
Character Composition Breakdown
Understanding the character composition of the string “Qkfzzu1lbnvinhp4dlhz” reveals a complex structure comprised of both alphabetic and numeric elements.
The string’s length is 20 characters, with varying character frequency among distinct letters and digits.
This intricate mix underscores the potential for diverse interpretations and applications, appealing to those who seek freedom in deciphering and utilizing such encoded information effectively.
Encoding Techniques Explored
Decoding the string “Qkfzzu1lbnvinhp4dlhz” involves a thorough examination of various encoding techniques that may have been employed to generate such a sequence.
Key encoding methods and data obfuscation strategies include:
- Base64 encoding
- URL encoding
- Hexadecimal representation
- Custom algorithms
Understanding these techniques is essential for unraveling the potential complexities behind the string’s construction and intended purpose.
Potential Meaning Interpretations
Analyzing the structure of the string “Qkfzzu1lbnvinhp4dlhz” reveals potential indicators of its encoding and intended meaning.
Through semantic analysis, one can discern patterns suggesting hidden messages embedded within the alphanumeric sequence.
The presence of varied character types may imply a complex layering of meaning, inviting further exploration into its cryptographic nature and potential applications in communication, data security, and information dissemination.
Possible Interpretations and Theories
The string “Qkfzzu1lbnvinhp4dlhz” presents opportunities for analysis through its potential cryptographic significance and cultural context.
Various interpretations may emerge from examining its encoding methods and historical relevance, shedding light on the underlying meanings.
As such, a systematic exploration of these dimensions may yield insights into the string’s purpose and implications.
Cryptographic Significance Explored
Cryptographic significance often hinges on the interpretation of encoded messages, such as Qkfzzu1lbnvinhp4dlhz. Various theories surrounding its meaning utilize advanced cryptographic techniques, influencing digital security protocols.
- Potential for data breaches
- Implications for privacy
- Relevance in cybersecurity
- Insights into encryption methods
These interpretations reflect a broader understanding of how encoded messages can affect the landscape of digital communication and protection.
Cultural Context Analysis
Encoded messages like Qkfzzu1lbnvinhp4dlhz can evoke diverse interpretations influenced by cultural contexts.
The analysis of cultural symbolism within digital communication reveals how meanings can shift based on societal norms and values.
Different groups may perceive the encoded message variably, reflecting their unique experiences and beliefs.
Thus, understanding these cultural underpinnings is essential for accurately decoding such cryptic communications.
Real-World Applications and Context
Applications of Qkfzzu1lbnvinhp4dlhz extend into various sectors, demonstrating its versatility beyond theoretical frameworks.
Its real-world applications and practical uses include:
- Enhancing data encryption methods
- Improving machine learning algorithms
- Streamlining supply chain logistics
- Facilitating advanced communication protocols
These implementations highlight the critical role of Qkfzzu1lbnvinhp4dlhz in driving innovation and efficiency across diverse industries, reflecting its significance in contemporary technology.
Expert Opinions and Insights
Expert opinions on Qkfzzu1lbnvinhp4dlhz reveal a consensus regarding its transformative potential across various fields. Experts emphasize its implications for digital cryptography, highlighting enhanced security protocols. Their analysis suggests that adoption could redefine data protection standards.
| Field | Potential Impact | Expert Analysis |
|---|---|---|
| Security Systems | Increased resilience | Redefines encryption methods |
| Data Privacy | Enhanced confidentiality | Protects user identity |
| Financial Transactions | Fraud reduction | Secures transactions |
The Future of Mysterious Digital Codes
How will the evolution of mysterious digital codes shape future technological landscapes? The advancement of digital encryption and code evolution promises to redefine security measures, data integrity, and user privacy.
Key aspects include:
- Enhanced cryptographic techniques
- Decentralized code systems
- Increased user autonomy
- Adaptive algorithms for evolving threats
These developments will empower individuals while ensuring robust protection against emerging cyber threats, fostering a landscape of digital freedom.
Conclusion
In conclusion, the enigmatic string Qkfzzu1lbnvinhp4dlhz encapsulates the essence of modern communication’s evolution, reminiscent of Da Vinci’s cryptic notes that concealed profound insights. Its intricate structure and potential interpretations highlight the burgeoning intersection of technology and expression, inviting further examination into its implications for data security and autonomy. As we navigate this digital labyrinth, the quest for understanding such codes may unveil new pathways in the ever-evolving landscape of information sharing, much like the Renaissance sparked innovation.




